Creating Tripwires
A step-by-step guide to creating tripwires from the dashboard for different detection scenarios.
No Account? No Problem
This guide covers creating tripwires from the dashboard. For document tripwires without an account, see Create Free Tripwire.
The Create Page
From the dashboard, click the "Create Tripwire" button in the top-right corner to open the dedicated creation page.
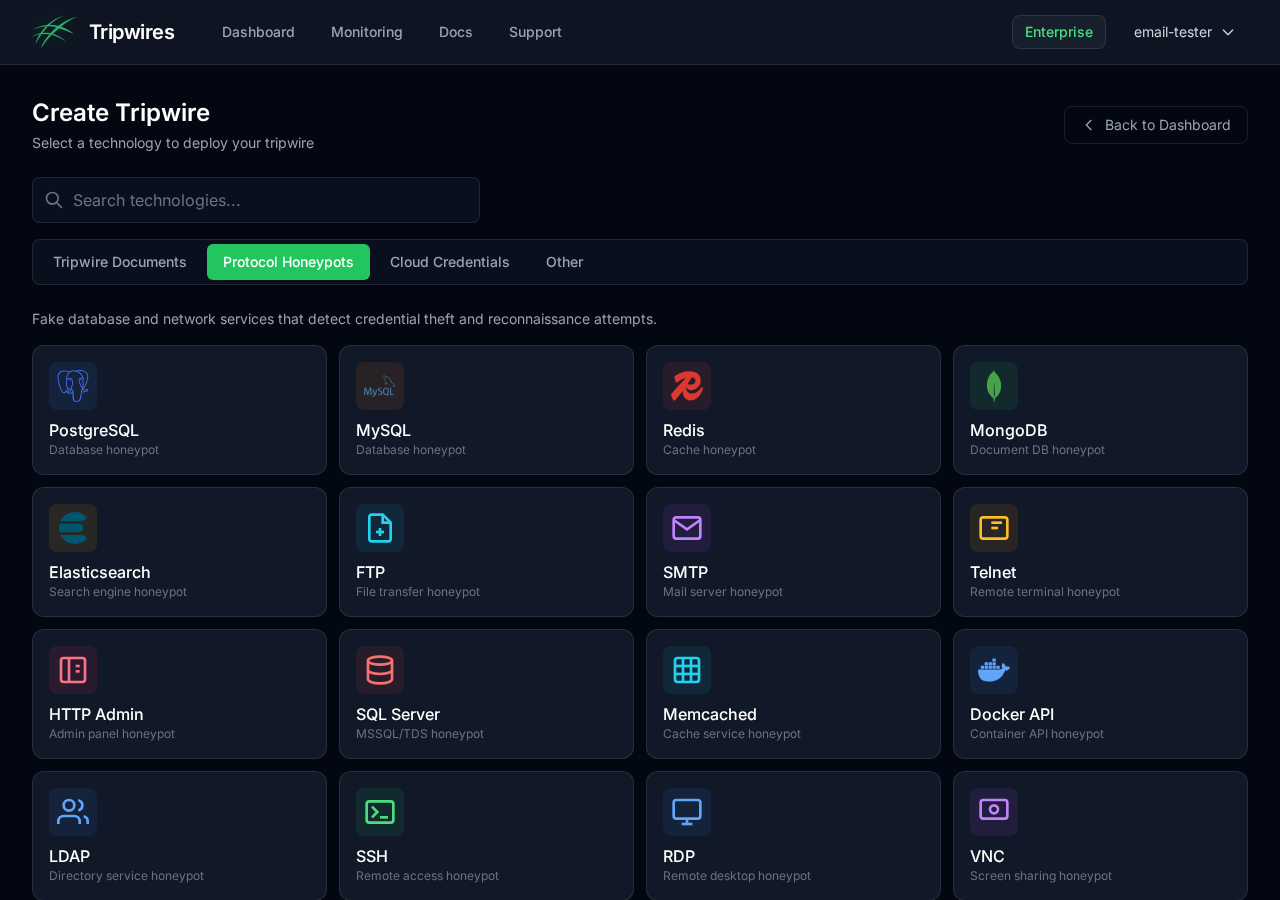
Choosing a Tripwire Type
The create page displays all available tripwire types organized by category. Use the tabs to switch between categories or the search bar to find a specific type:
Protocol Honeypots
These tripwires generate fake service credentials that trigger alerts when someone attempts to connect:
Tripwire Documents
These tripwires are downloadable files that trigger alerts when opened:
Cloud Credentials
Generate fake cloud provider API keys that alert when used:
QR Codes
QR codes for physical security that trigger when scanned:
Print and place on physical assets - server rooms, equipment, documents
Naming Your Tripwire
After selecting a type, you'll be prompted to enter a name. Choose a descriptive name that helps you:
- Identify the purpose - Where will these credentials be planted?
- Remember the context - What system or environment does it represent?
- Recognize in alerts - When triggered, you'll want to know immediately what was accessed
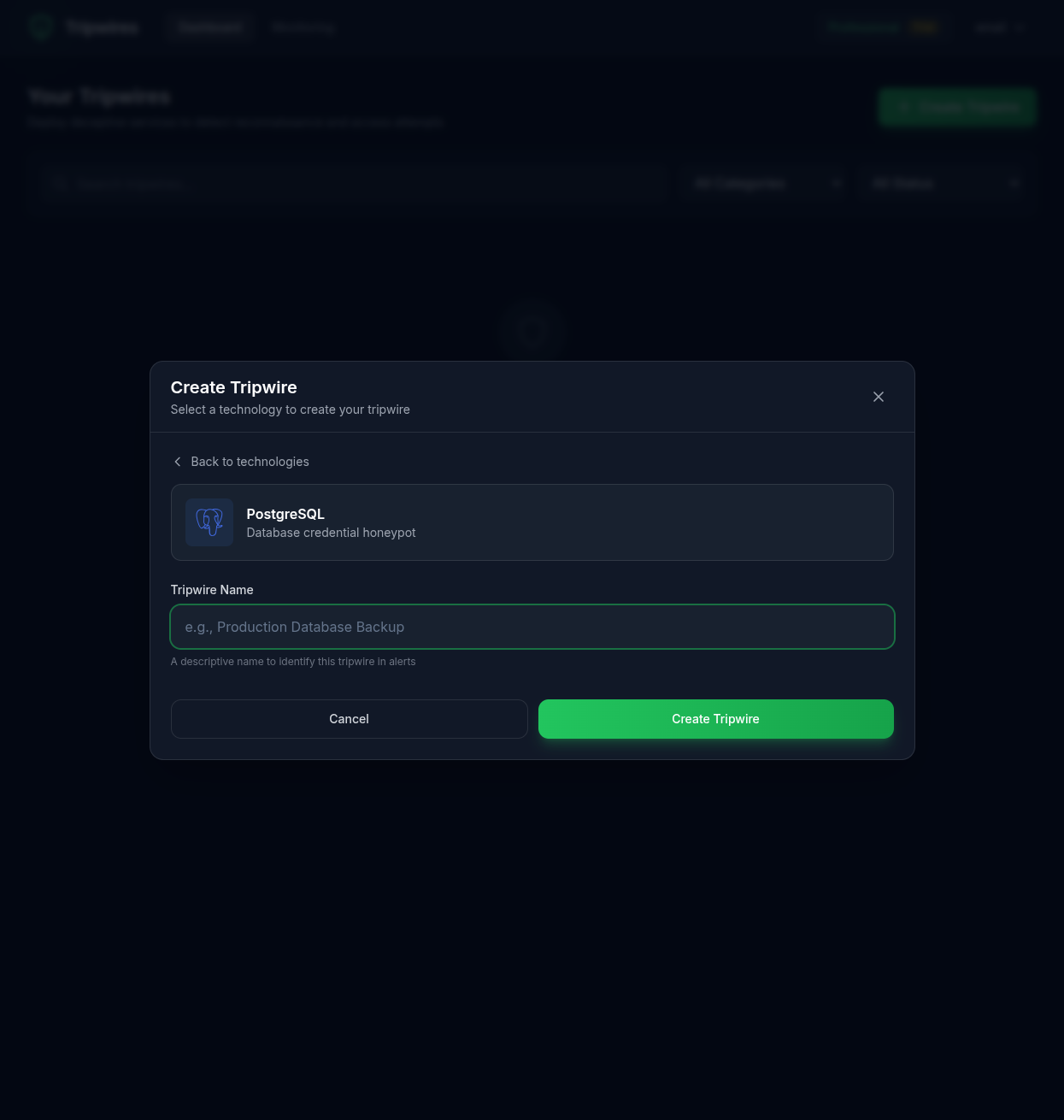
Naming Best Practices
Good Names
- ✓ Production Database Backup
- ✓ AWS Staging Redis
- ✓ Customer Data Warehouse
- ✓ Jenkins CI MongoDB
Avoid
- ✗ Test
- ✗ DB1
- ✗ Honeypot (too obvious)
- ✗ Fake credentials (too obvious)
Creating the Tripwire
Click "Create Tripwire" to generate the tripwire. The system will:
- Generate a unique hostname for your honeypot
- Create randomized, realistic-looking credentials
- Configure the detection endpoint
- Activate monitoring immediately
After Creation
Once created, you'll be redirected to the tripwire details page where you can view and copy the generated credentials. See the Tripwire Details documentation for more information.
Important Security Note
Tripwire credentials are designed to look realistic. Make sure your team knows which credentials are honeypots to avoid accidentally triggering alerts during legitimate operations.