Redis Honeypot
Detect unauthorized access attempts targeting Redis cache and data stores.
About Redis
Redis is an in-memory data structure store used as a database, cache, and message broker. Its speed and versatility make it popular for session storage, caching, and real-time analytics. Compromised Redis instances can leak session tokens, cached data, and provide lateral movement opportunities.
What Gets Captured
When an attacker attempts to connect using your Redis honeypot credentials, Tripwires captures:
- AUTH password - The password used in the AUTH command
- Source IP - The attacker's IP address
- Timestamp - Exact time of the connection
- Commands attempted - Any Redis commands sent
Connection String Formats
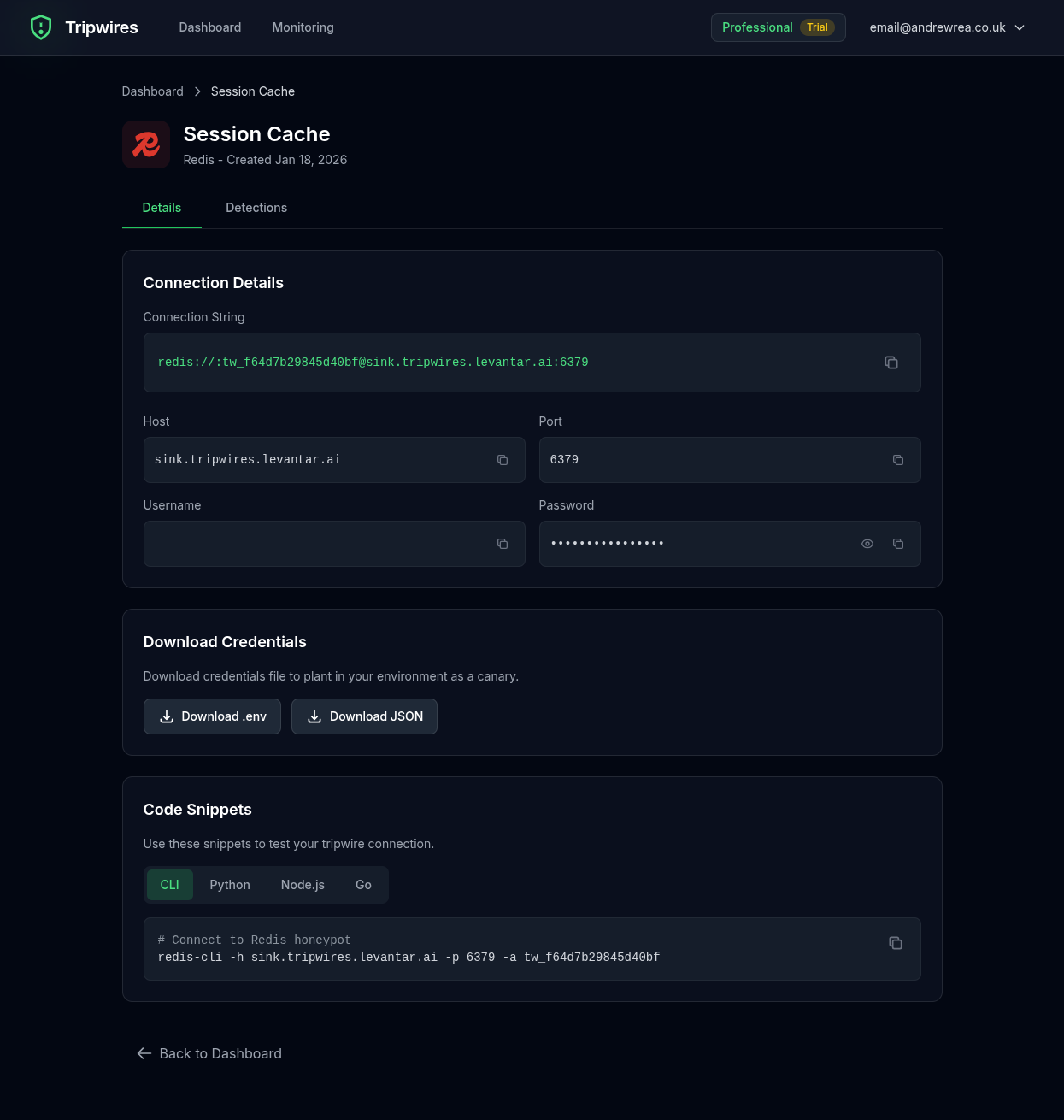
Standard Connection URL
redis://:password@redis-xxx.gettripwires.com:6379redis-cli Command
redis-cli -h redis-xxx.gettripwires.com -a passwordPython (redis-py)
import redis
r = redis.Redis(
host='redis-xxx.gettripwires.com',
port=6379,
password='password'
)Node.js (ioredis)
const Redis = require('ioredis');
const redis = new Redis({
host: 'redis-xxx.gettripwires.com',
port: 6379,
password: 'password'
});Strategic Placement Ideas
Session Store Configuration
Leave as "old session cache" credentials in application configs.
Sidekiq/Resque Settings
Add as "backup queue server" in job processor configuration.
Docker Compose Files
Include in old docker-compose.yml.bak files.
High-Value Target
Redis instances are frequently targeted because they often contain session tokens, cached authentication data, and can be used for code execution if misconfigured.