PostgreSQL Honeypot
Detect unauthorized access attempts targeting PostgreSQL databases.
About PostgreSQL
PostgreSQL is one of the most popular open-source relational databases, widely used in production environments from startups to enterprises. Its prevalence makes PostgreSQL credentials a high-value target for attackers.
What Gets Captured
When an attacker attempts to connect using your PostgreSQL honeypot credentials, Tripwires captures:
- Username - The username sent in the connection attempt
- Source IP - The attacker's IP address
- Timestamp - Exact time of the connection
- Database name - The database they tried to access
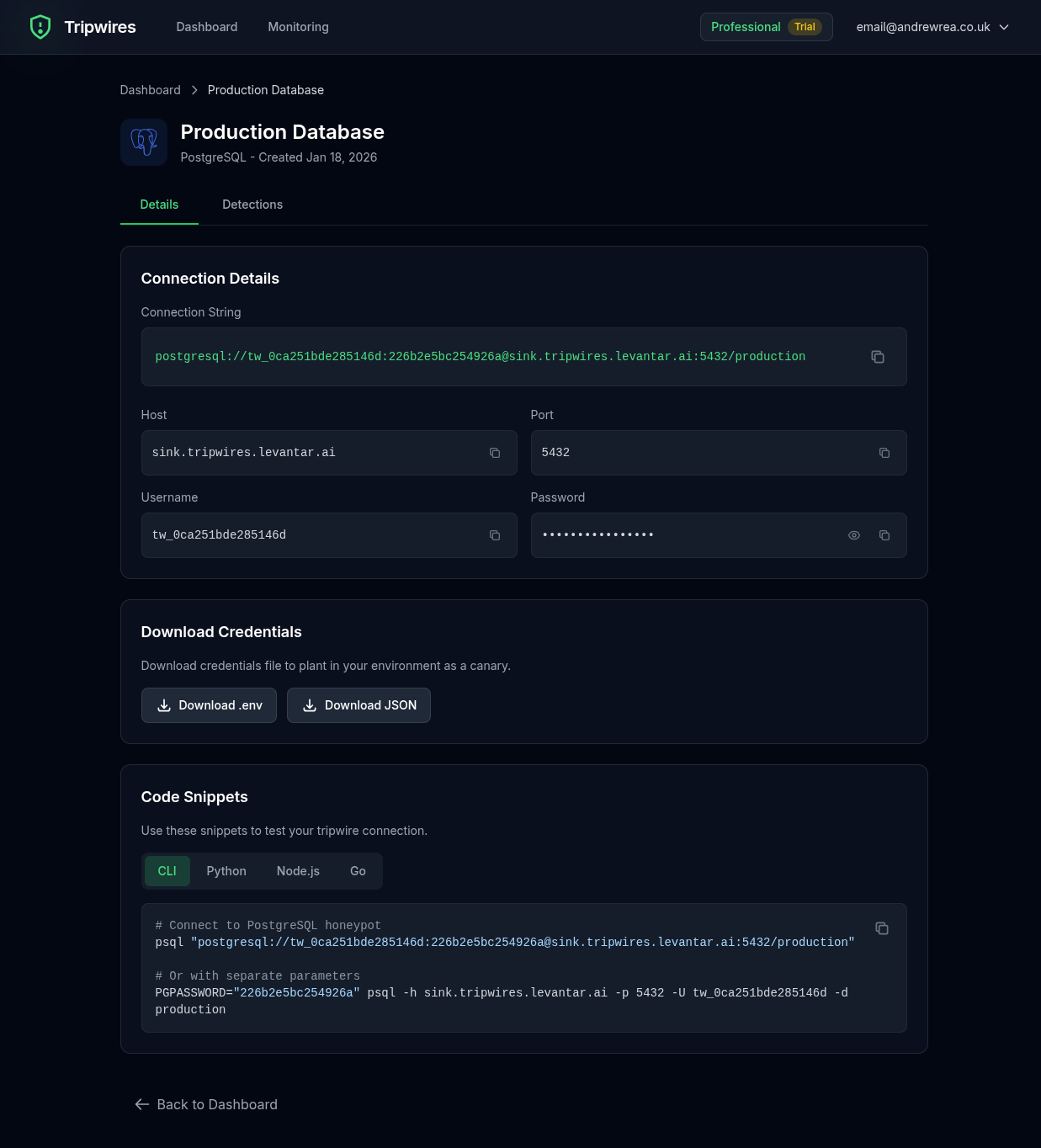
Connection String Formats
PostgreSQL credentials can be planted in various formats depending on your tech stack:
Standard Connection URL
postgresql://user:password@pg-xxx.gettripwires.com:5432/dbnamepsql Command
psql -h pg-xxx.gettripwires.com -U user -d dbnameEnvironment Variables
PGHOST=pg-xxx.gettripwires.com
PGPORT=5432
PGUSER=user
PGPASSWORD=password
PGDATABASE=dbnameRails database.yml
production:
adapter: postgresql
host: pg-xxx.gettripwires.com
port: 5432
username: user
password: password
database: dbnameStrategic Placement Ideas
Database Migration Scripts
Add as commented "production backup" credentials in migration directories.
CI/CD Configuration
Leave as "deprecated" database URL in old pipeline configs.
Developer Notes
Include in internal documentation as "legacy database" connection info.