🐬
MySQL Honeypot
Detect unauthorized access attempts targeting MySQL databases.
3306
Default Port
TCP
Protocol
Username
Detection
About MySQL
MySQL is the world's most popular open-source relational database, powering countless web applications from WordPress to large-scale enterprise systems. Its widespread use makes MySQL credentials extremely attractive to attackers.
What Gets Captured
When an attacker attempts to connect using your MySQL honeypot credentials, Tripwires captures:
- Username - The username sent in the connection attempt
- Source IP - The attacker's IP address
- Timestamp - Exact time of the connection
- Database name - The database they tried to access
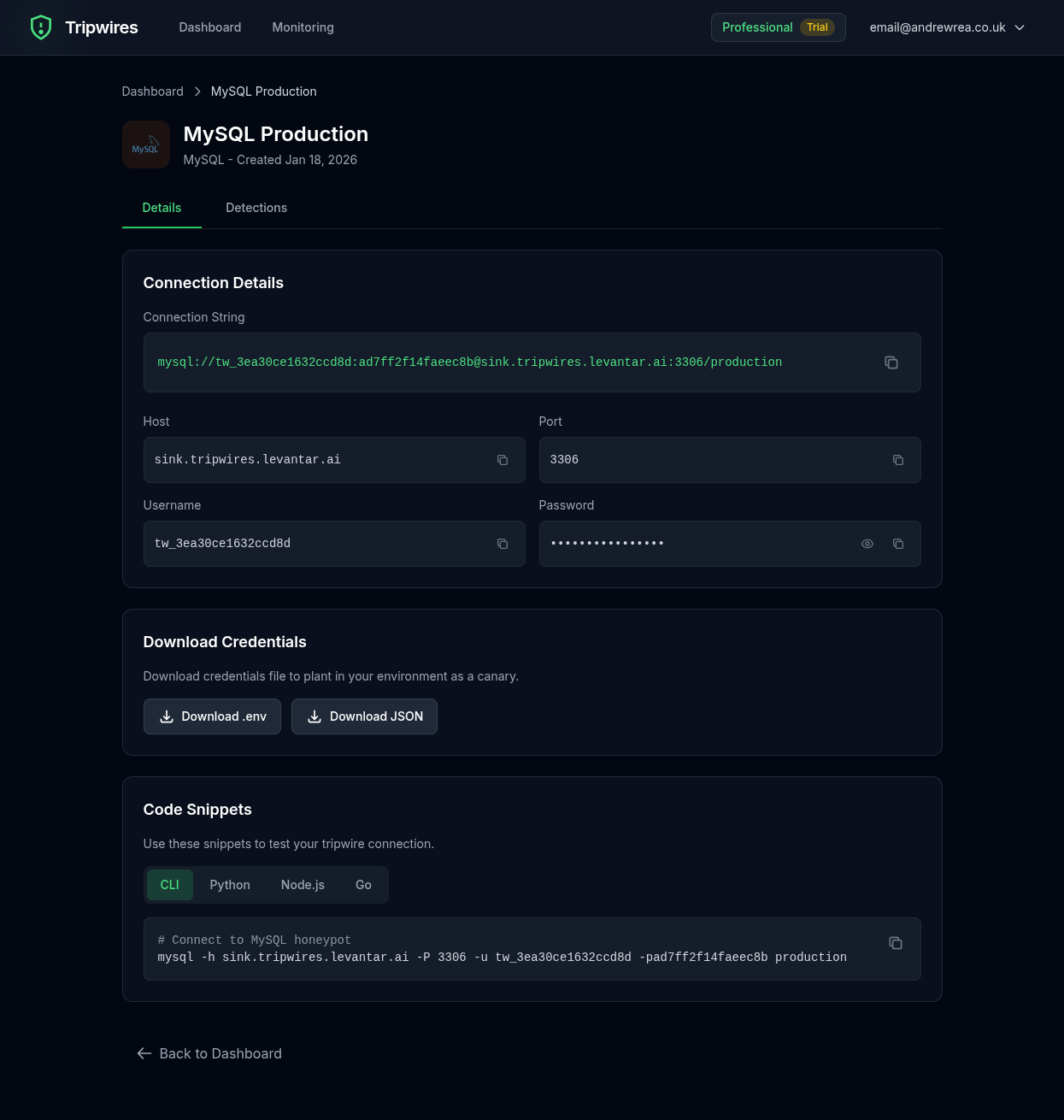
Connection String Formats
Standard Connection URL
mysql://user:password@mysql-xxx.gettripwires.com:3306/dbnamemysql Command
mysql -h mysql-xxx.gettripwires.com -u user -p dbnamePHP PDO
$dsn = 'mysql:host=mysql-xxx.gettripwires.com;dbname=dbname';
$pdo = new PDO($dsn, 'user', 'password');WordPress wp-config.php
define('DB_NAME', 'dbname');
define('DB_USER', 'user');
define('DB_PASSWORD', 'password');
define('DB_HOST', 'mysql-xxx.gettripwires.com');Strategic Placement Ideas
WordPress Backups
Leave in old wp-config.php.bak files that might be discovered.
Database Dump Scripts
Include in shell scripts used for database backups.
Development Environment Files
Add as "staging database" in .env.development files.