SMTP Honeypot
Detect unauthorized access attempts targeting mail servers.
About SMTP
SMTP (Simple Mail Transfer Protocol) is the standard protocol for sending email. SMTP credentials are highly valuable to attackers for sending phishing emails, spam, or accessing email communications. Compromised mail servers can also be used for business email compromise (BEC) attacks.
What Gets Captured
When an attacker attempts to authenticate using your SMTP honeypot credentials, Tripwires captures:
- Username - The AUTH LOGIN username
- Source IP - The attacker's IP address
- Timestamp - Exact time of the connection
- Auth method - The authentication mechanism used
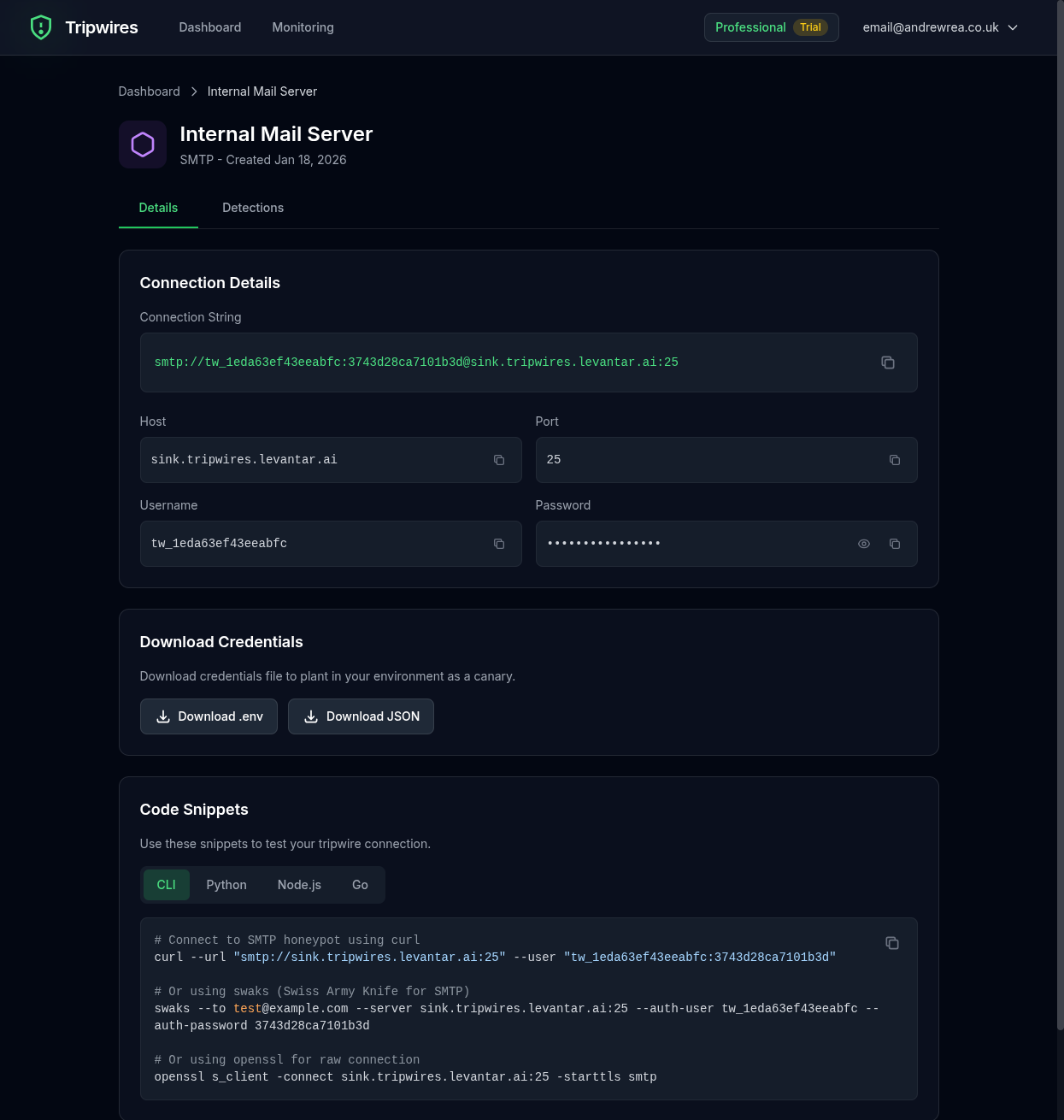
Connection String Formats
Standard SMTP URL
smtp://user:password@smtp-xxx.gettripwires.com:587swaks (SMTP testing tool)
swaks --to test@example.com \
--server smtp-xxx.gettripwires.com:587 \
--auth LOGIN \
--auth-user user \
--auth-password passwordPython (smtplib)
import smtplib
server = smtplib.SMTP('smtp-xxx.gettripwires.com', 587)
server.starttls()
server.login('user', 'password')Node.js (nodemailer)
const nodemailer = require('nodemailer');
const transporter = nodemailer.createTransport({
host: 'smtp-xxx.gettripwires.com',
port: 587,
auth: {
user: 'user',
pass: 'password'
}
});Strategic Placement Ideas
Application Email Config
Leave as "notification service" credentials in app config files.
CI/CD Notification Settings
Add as "alert email server" in deployment pipelines.
Internal Monitoring Tools
Include in monitoring system email alert configurations.
High-Impact Target
Compromised SMTP credentials enable attackers to send emails appearing to come from your organization, making them extremely dangerous for phishing and business email compromise attacks.