Welcome to Tripwires
Learn how to deploy invisible tripwires across your infrastructure to detect unauthorized access the moment it happens.
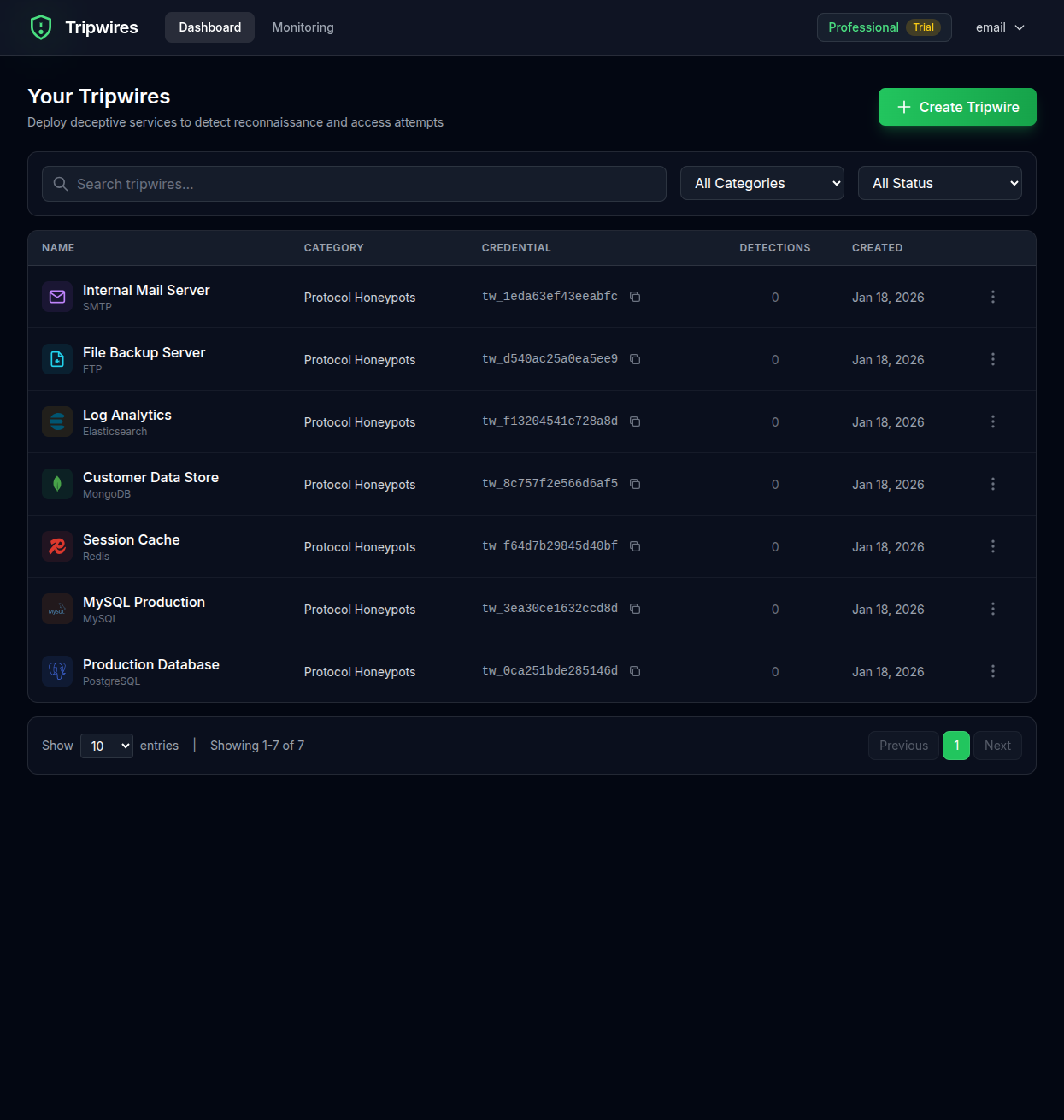
What are Tripwires?
Tripwires are invisible security mechanisms that detect when attackers access sensitive areas of your infrastructure. Unlike traditional security tools that generate mountains of logs, tripwires have a zero false positive rate - they only alert when someone actually accesses the bait.
Instant Alerts
Get notified within seconds when a tripwire is triggered.
Zero False Positives
Every alert indicates real unauthorized access.
Easy Setup
Deploy tripwires in minutes without any code changes.
Types of Tripwires
Tripwires supports multiple detection methods to cover different attack vectors:
| Type | Use Case | What It Detects |
|---|---|---|
| Protocol Honeypots | Credential theft, lateral movement | Connection attempts across 17 protocols (databases, SSH, RDP, SMTP, and more) |
| Tripwire Documents | Data exfiltration, insider threats | Document opens |
| Cloud Credentials | Cloud infrastructure breaches | AWS API key usage |
| QR Codes | Physical security, asset tracking | QR code scans |
Getting Started
There are two ways to get started with Tripwires:
Option A: Try It Free
Create document tripwires instantly with no account required. Just provide your email for alerts.
Create free tripwires →Option B: Create an Account
Full access to all 17 protocol honeypots, cloud credentials, and the management dashboard.
Quick start guide →Next Steps
Continue to the Quick Start guide for a step-by-step walkthrough of creating your first tripwire with an account, or create a free tripwire instantly without signing up.