MongoDB Honeypot
Detect unauthorized access attempts targeting MongoDB document databases.
About MongoDB
MongoDB is the most popular NoSQL document database, widely used for applications requiring flexible schemas and high scalability. Its prevalence in modern web applications makes MongoDB credentials valuable targets for attackers seeking customer data or application access.
What Gets Captured
When an attacker attempts to connect using your MongoDB honeypot credentials, Tripwires captures:
- Username - The username in the authentication attempt
- Source IP - The attacker's IP address
- Timestamp - Exact time of the connection
- Database name - The database they tried to access
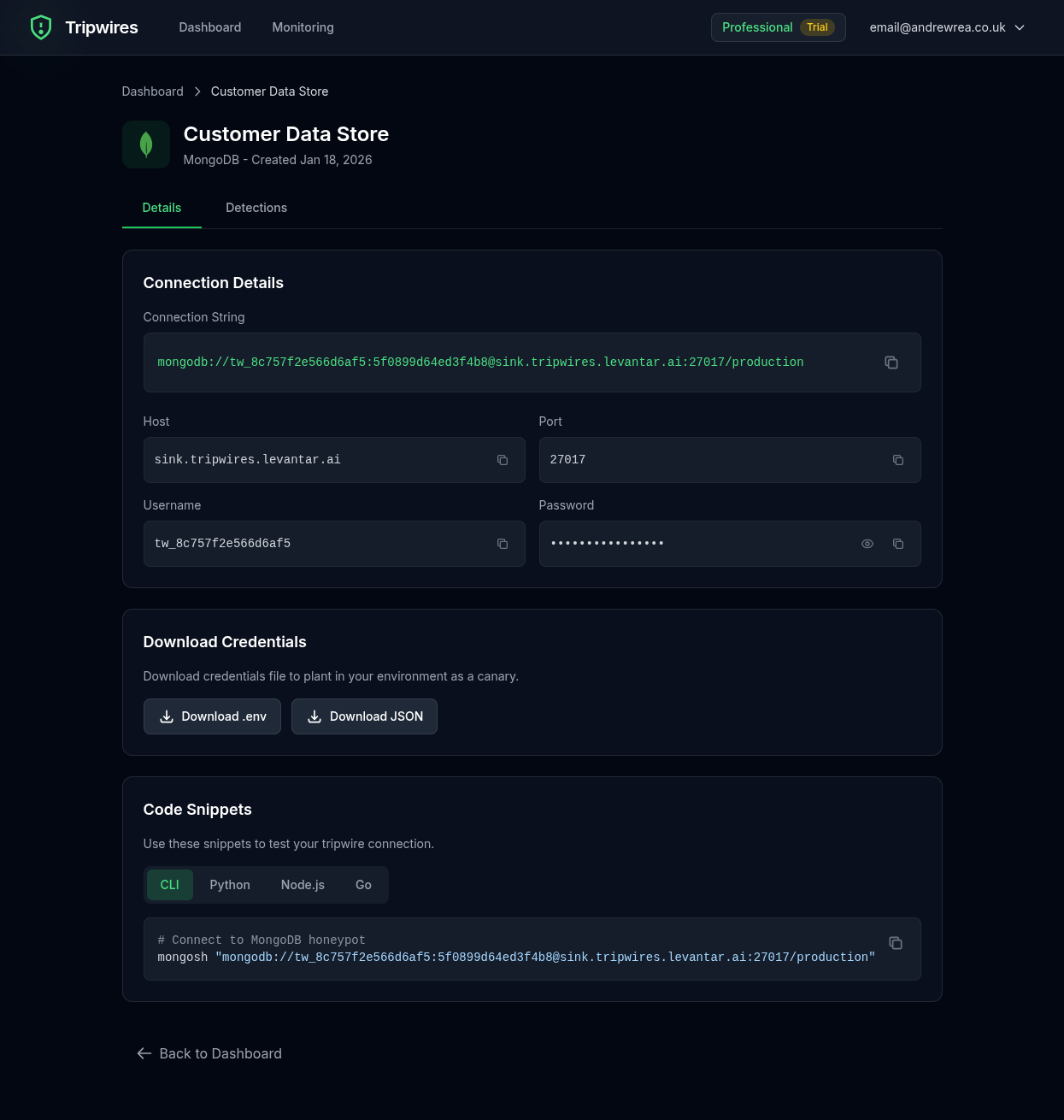
Connection String Formats
Standard Connection URL
mongodb://user:password@mongo-xxx.gettripwires.com:27017/dbnamemongo Shell
mongo "mongodb://mongo-xxx.gettripwires.com:27017/dbname" -u user -p passwordNode.js (mongoose)
const mongoose = require('mongoose');
mongoose.connect('mongodb://user:password@mongo-xxx.gettripwires.com:27017/dbname');Python (pymongo)
from pymongo import MongoClient
client = MongoClient('mongodb://user:password@mongo-xxx.gettripwires.com:27017/dbname')Strategic Placement Ideas
Application Configuration
Leave as "analytics database" credentials in config files.
Microservices Config
Add as "user-service database" in kubernetes secrets files.
Data Migration Scripts
Include in scripts that appear to migrate customer data.