FTP Honeypot
Detect unauthorized access attempts targeting FTP file servers.
About FTP
FTP (File Transfer Protocol) is a legacy protocol still widely used for file transfers, especially in enterprise environments, backup systems, and content publishing workflows. Despite newer alternatives, FTP credentials remain valuable to attackers for accessing file shares and backup data.
What Gets Captured
When an attacker attempts to connect using your FTP honeypot credentials, Tripwires captures:
- Username - The USER command value
- Source IP - The attacker's IP address
- Timestamp - Exact time of the connection
- Commands - FTP commands attempted
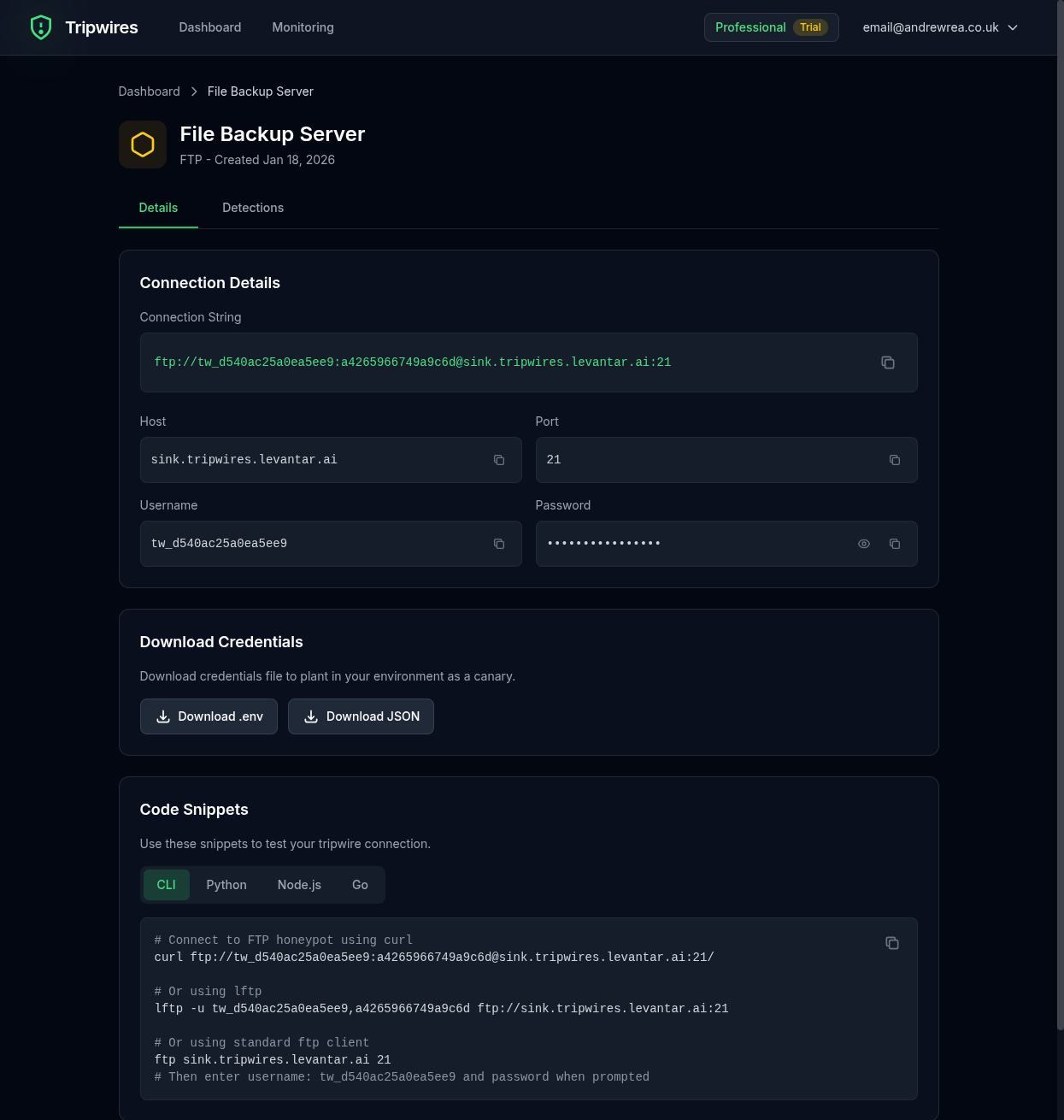
Connection String Formats
Standard FTP URL
ftp://user:password@ftp-xxx.gettripwires.com:21ftp Command
ftp ftp-xxx.gettripwires.com
Username: user
Password: passwordlftp Command
lftp -u user,password ftp-xxx.gettripwires.comBackup Script
#!/bin/bash
# Backup script - DO NOT DELETE
FTP_HOST="ftp-xxx.gettripwires.com"
FTP_USER="user"
FTP_PASS="password"
ncftp -u $FTP_USER -p $FTP_PASS $FTP_HOST << EOF
cd /backups
put database.sql.gz
quit
EOFStrategic Placement Ideas
Backup Scripts
Leave in cron job scripts that appear to upload backups.
CMS Publishing Config
Add as "web server deployment" credentials in publishing tools.
Legacy System Documentation
Include in documentation for "file server" access.
Legacy Systems
FTP honeypots are especially effective in environments with legacy systems, as attackers often specifically target older protocols that may have weaker security configurations.